Data Loss Prevention (DLP) based on policies was built for a world that no longer exists.
For decades, security teams have relied on policies that looked sound on paper. In practice, translating them into DLP rule sets has meant a constant struggle between false positives that disrupt business and missed incidents that expose sensitive data.
As the use of generative AI tools rapidly increases, so does the threat of data loss. Employees paste proprietary code into chatbots, upload customer data into AI-powered marketing tools, and rely on copilots embedded into everyday SaaS platforms – often without security review.
This new reality, often called Shadow AI, refers to the unsanctioned or unmanaged use of AI tools by employees – without formal security review, governance, or contractual safeguards. It is not necessarily malicious – in fact, it is often driven by productivity. But when sensitive enterprise data is introduced into AI systems that the organization does not control, visibility is lost, and traditional DLP controls become ineffective.
Shadow AI exposes a critical weakness: policy-reliant DLP cannot keep pace with AI-driven workflows.
This article is a shortened version based on a white paper we recently published in collaboration with CISO Tradecraft. The full version is available here.
Past: How We Got Here
Traditional DLP began with simple keyword filtering – static “dirty word lists” designed to catch sensitive terms moving across network chokepoints. In an era of mostly unencrypted traffic and predictable data flows, basic string matching and file hashes were often enough.
As regulatory pressure increased in the early 2000s, DLP evolved into content-aware inspection. Regex-based detection enabled teams to identify structured data such as credit card and Social Security numbers. While more sophisticated, these systems still relied on predefined patterns – generating high false positives and struggling with context.
Then came widespread encryption after the Snowden disclosures. HTTPS became the norm, forcing organizations to deploy proxy-based inspection tools just to regain visibility. Meanwhile, insider risks and endpoint data movement remained largely unaddressed.
With the migration to the cloud, CASB solutions emerged to enforce policy across SaaS platforms. But agent gaps, BYOD environments, and expanding cloud ecosystems made enforcement inconsistent and incomplete.
At every stage, DLP adapted incrementally, but always remained policy-driven, perimeter-focused, and dependent on predicting how data might leave the organization.
That model was already strained, and then AI arrived.
Present: The State of DLP, and the Age of AI
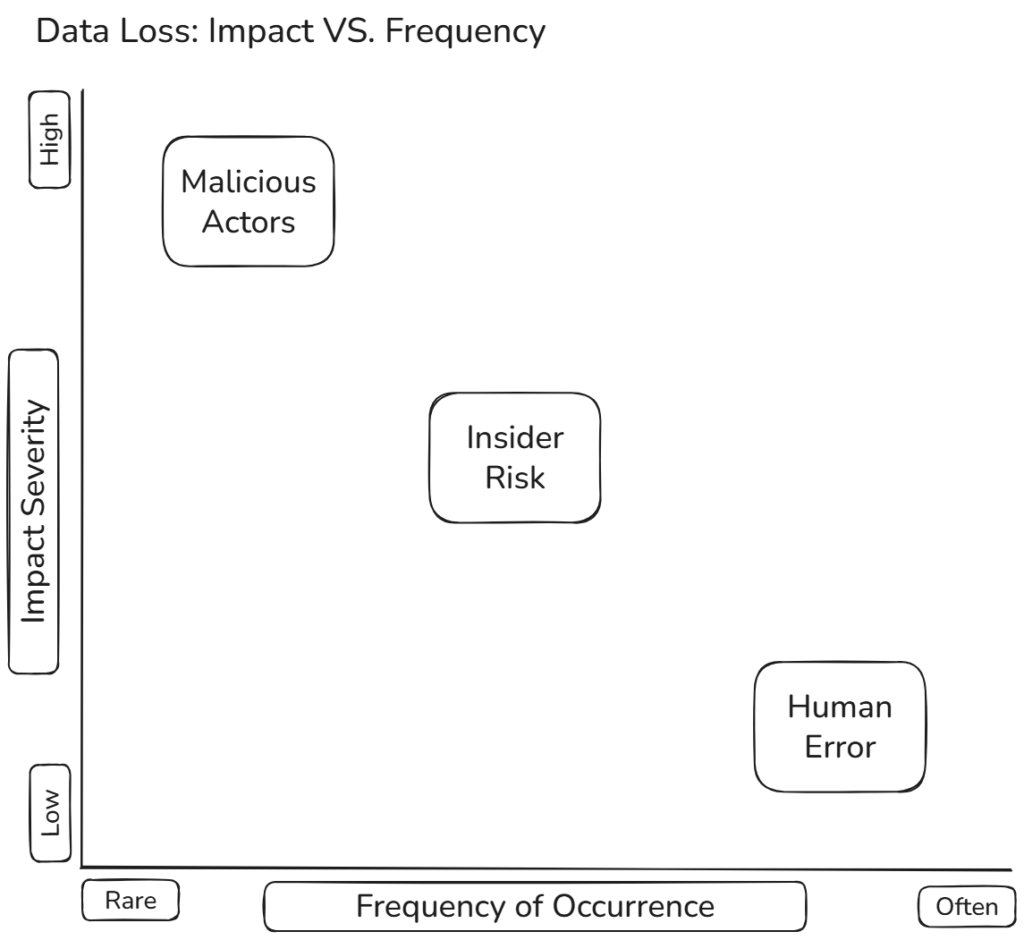
Traditional DLP was already showing cracks before AI came into the picture. Modern enterprises generate vast amounts of structured and unstructured data across endpoints, SaaS platforms, cloud storage, and collaboration tools. Manually translating all possible data flows, users, and destinations into static policies is no longer scalable. The result is familiar to every security team: overwhelming false positives, missed incidents, and rising operational costs.
AI made the problem ever more complex.
Tools like Microsoft Copilot, ChatGPT, Claude, and Gemini are being embedded into everyday workflows – sometimes enabled by default. These systems don’t just move data; they interpret, synthesize, and recombine it. They operate through dynamic prompts, contextual conversations, and encrypted channels that bypass traditional inspection methods.
Sensitive data is no longer exfiltrated only through file attachments or obvious pattern matches. It is pasted into conversational prompts, indexed by AI copilots, and transmitted to systems outside the enterprise boundary. Once submitted to an external AI platform, often without contractual safeguards, organizations lose visibility and control over how that data is retained, processed, or reused.
Blocking AI outright is rarely effective. Employees find workarounds, productivity suffers, and security teams lose what little visibility they had. Yet allowing unrestricted use exposes organizations to regulatory violations, intellectual property loss, and reputational damage. Compliance frameworks do not distinguish between malicious exfiltration and accidental disclosure.
Monitoring traffic alone is no longer enough. By the time a violation is detected, the data may already be gone.
This is the core problem: policy-based DLP was designed to match patterns and enforce rules. AI-driven workflows require understanding context, intent, and behavior – in real time.
Future: Using AI to Contain AI
AI-driven workflows are here to stay, and our security models must evolve accordingly.
The answer is not more policies (no matter how polished or automated), but rather a shift from static enforcement to context-aware protection. Modern approaches leverage AI to understand data flows across endpoints, SaaS platforms, email, storage, and web interactions – automatically classifying both structured and unstructured data by sensitivity, not just format.
Instead of trying to predict every possible exfiltration scenario in advance, these systems learn what normal business behavior looks like. They evaluate who is sharing data, what is being shared, where it’s going, and whether that action aligns with legitimate business intent – in real time.
This allows organizations to enable AI adoption safely rather than attempting to block it outright. The goal is not to slow innovation, but to ensure that sensitive data moves responsibly within AI-powered environments.
For leadership, the imperative is clear: legacy DLP and passive monitoring cannot protect a modern enterprise. Compliance requirements are tightening, financial penalties are rising, and AI usage is accelerating. The only sustainable path forward is to deploy intelligent, adaptive controls capable of operating at the speed and scale of AI.
Shadow AI is not a theoretical risk – it is already embedded in everyday business operations. The organizations that adapt their security models now will be the ones that innovate confidently, without sacrificing control.
The question is no longer whether AI will be used inside your organization, but whether your security architecture is prepared for it.
If you’re evaluating how to modernize DLP for the AI era, we encourage you to read the full white paper and explore what context-aware, AI-driven data protection looks like in practice.